Stay ahead of the curve with the latest news, ideas and resources on all things Identity Assurance and Passwordless.
3 Things Stopping You from Going Passwordless



We’ve had the privilege of observing companies across the globe successfully eliminate passwords for their customers and employees. These trailblazers have set the standard and demonstrated the benefits unlocked by passwordlesss authentication. Some of the key ingredients include a clear understanding of Why they are moving beyond passwords as well as a willingness to trust their partners in defining the How.
I’ve also seen less fortunate companies who have hit road blocks.
Despite having a strong desire to deploy next-gen security some organizations can’t seem to get out of their own way. Some developed massive RFI’s that went nowhere. Others had “passwordless initiatives” that began in 2018, got bogged down by identity orchestration projects, and are just now finally deploying 14-character complex passwords (seriously).
These unfortunate situations have some things in common. Here are the top 3 things we’ve seen get in the way of a passwordless deployment and how you can avoid them:
1. Expecting your Identity Provider to Get You There
If you think your incumbent Identity Provider (IdP) is going to eliminate all of your passwords, I’ve got news for you.
Legacy Identity Platforms were built on top of passwords and password-based MFA. While the IAM giants did an incredible job and revolutionized digital security, the elimination of passwords and shared secrets is not their core competency. In fact, authentication itself has always been an add-on feature for the IdP. There has been no need to invest significant resources in improving authentication. As a result, very little innovation has happened on that front.
Just look at the 2020 Gartner Magic Quadrant for IAM. Why is the “Visionaries” quadrant empty?
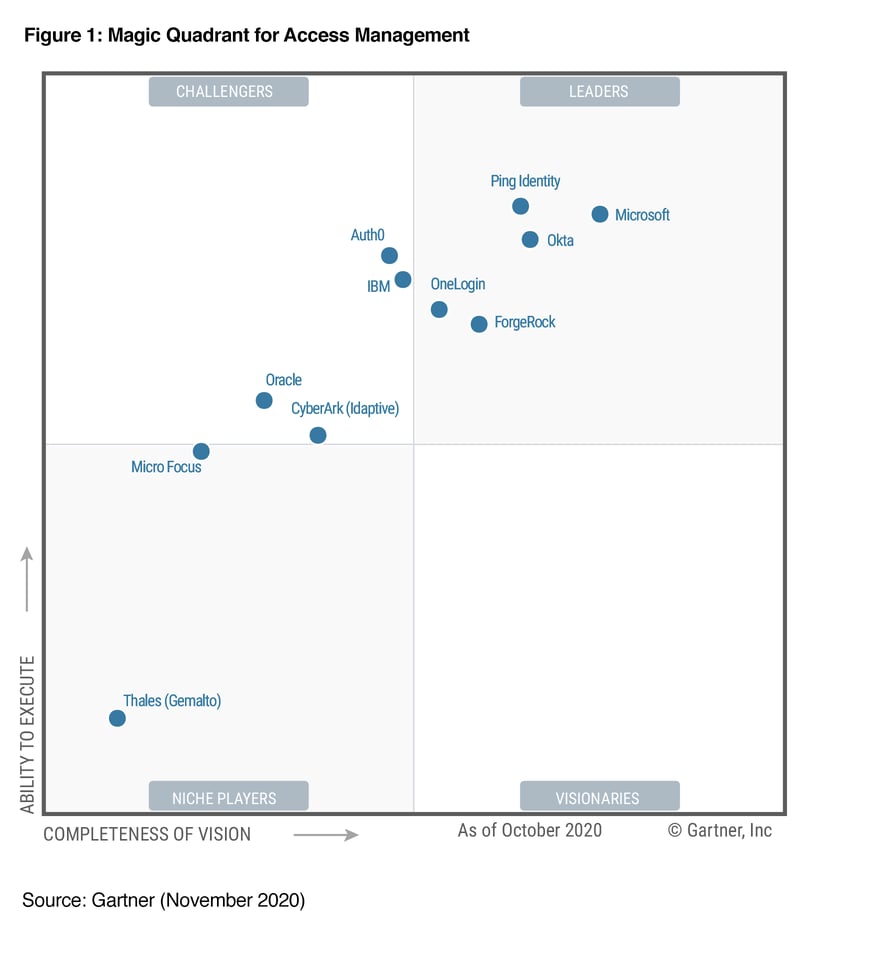
The lack of focus and innovation is why we are seeing more and more businesses Decoupling Authentication from Identity. After years of waiting for next-gen authentication to arrive and reading blog post after blog post about the benefits of passwordless, these customers are left scratching their heads when they realize their IdP is still using passwords… everywhere.
Fortunately, a growing number of organizations have wised up to the differences between passwordless marketing and passwordless MFA. Those who have succeeded at this mission are teams that realized that they cannot evolve beyond passwords if they simply rely on their incumbent Identity Providers.
2. Letting Perfect Be the Enemy of Great
“We need everyone to be able to use the same authentication method everywhere, under all conditions, on day 1.”
This one-size-fits-all mindset often appears in large, complex organizations who are (rightfully) trying to eliminate passwords for all users. It is commendable to see project leaders striving to satisfy all use cases & edge cases on day 1.
Unfortunately, carpet-bombing the password never works. The actual process is more like mowing a lawn, one section at a time, until all of the grass looks consistent.

For an enterprise, the Passwordless transformation is similar to a cloud transformation. It moves incrementally and addresses the needs of a diverse array of user devices, applications and edge cases. These variables manifest in a number of ways:
- Users’ personal preferences will vary. Many people are glued to their smartphone. Some prefer to use their desktop for everything work-related.
- Some users have an old phone, or no phone. Complex environments have widely different device populations and compliance requirements.
- Highly regulated departments might disallow smartphones and require the use of a hardware security token.
- And of course, many users simply do not want to carry another piece of hardware.
See why the one-size-fits all approach fails? Trying to solve every use case and edge case on day 1 is an absolutist pursuit of perfection.
These organizations take advantage of the various passwordless login methods that satisfy the needs of every situation. Your MFA strategy should allow for the use of Mobile-initiated Authentication, FIDO2 Security Tokens, and native authenticators such as Windows Hello:
The successful passwordless companies are those who focus on a progressive rollout as outlined in our Free Guide to Password Elimination.
Don’t let perfect be the enemy of great. Focus on mowing the password lawn.
3. IT and Security Teams Who Are Not on the Same Page
The alignment of teams is critical to the success of a transformational project. Many IT initiatives have slowed down to a halt when departments don’t see eye to eye or have conflicting agendas. Any meaningful workforce transformation depends on your IT and Help desk becoming supportive champions of the project.
This is where my earlier point about emphasizing the “Why” comes into play.
Going passwordless brings a tremendous benefit in terms of user experience, increased security, and cost savings. These impacts are immediately felts across the organization as the drop in password-related support tickets improves the lives of IT, Help desk, and support teams. These groups are the foundation for any successful authentication initiative and they must understand why it is happening and how they can benefit.
The good news is Passwordless MFA has a habit of bringing departments together. Rarely do you see IT, InfoSec, Fraud, Compliance, and Line of Business teams come together with such a passion for a common goal. We have seen some of the most fragmented teams build long-lasting bonds over the success of a passwordless deployment.

To Get Rid of Passwords, You have to Think Like a Password
No, not really. But getting it right means adopting the passwordless mindset. Here is a summary of what the Passwordless Companies are doing:
- Go passwordless on your terms. Don’t sit around waiting for your incumbent IAM provider to eliminate passwords (they won’t), and don’t let legacy vendors dictate what passwordless identity should mean to you.
- Don’t let perfect be the enemy of great. Focus on quick wins with one user group at a time as you progress towards a passwordless state.
- Align your teams towards a common goal. Passwordless MFA sells itself. Nobody wants to go back to passwords. Focus on why password elimination matters to your colleagues and it will naturally accelerate on its own.
Bojan Simic
CEO, HYPR
Bojan Simic is the Chief Executive Officer & Co-Founder of HYPR. Bojan's vision for the elimination of shared secrets and his experience in authentication & cryptography serves as the underlying foundation for HYPR technology and company strategy. Previously, he served as an information security consultant for Fortune 500 enterprises in the financial and insurance verticals conducting security architecture reviews, threat modeling, and penetration testing. Bojan has a passion for deploying applied cryptography implementations across security-critical software in both the public and private sectors. Bojan also serves as HYPR’s delegate to the FIDO Alliance board of directors, empowering the alliance’s mission to rid the world of passwords.
Related Content